You didn't share your password. You didn't click anything suspicious. But someone, somewhere, is reading your messages right now.
It started with a text from a cousin.
"Hey, did you send me that link asking me to vote for you in some competition?"
Amina hadn't sent any link. She hadn't entered any competition. She opened her Facebook — and her stomach dropped. Three messages sent at 2 AM. A post she'd never written. A friend request accepted for a person she had never seen in her life. Someone had been inside her account for who knows how long, moving around quietly, using her name, her face, her trust.
This isn't a story from a movie. It's a scenario playing out in Dar es Salaam, Nairobi, Kampala, and Kigali every single day. And the most terrifying part? Most people have no idea it's happening — until it's too late.
Why This Is More Common Than You Think
Here's a number that should make you put your phone down for a second: according to a 2025 INTERPOL Africa Cyberthreat Assessment Report, cybercrime now accounts for more than 30% of all reported crimes in Eastern Africa. Not pickpocketing. Not fraud at the market. Cybercrime.
In some African countries, suspected scam notifications rose by up to 3,000% in a single year, according to data from Kaspersky. Meanwhile, the FTC reported $1.9 billion in social media scam losses in 2024 alone — an 870% increase from just five years earlier.
We are living through the golden age of account hijacking. And East Africa, with its fast-growing internet adoption, booming mobile money ecosystem, and historically low cybersecurity awareness, has become a prime hunting ground.
The good news? Checking whether someone is inside your accounts takes less than five minutes. You just need to know where to look.
The Sneaky Ways They Get In
Before we go looking for intruders, it helps to understand how they walk through the front door in the first place.
The "OMG, is this you?" message. You've seen it. A friend sends you a WhatsApp or Facebook message with a link — "I saw this video of you, haha!" You click it. A fake login page appears. You type your details. And just like that, someone in another city has your password. This is phishing, and it remains the most common form of cybercrime on the continent.
Your password was already stolen — just not from you. This one is unsettling. Large companies get hacked all the time — their databases, containing millions of usernames and passwords, get dumped online. If you use the same password across multiple platforms (and 80% of breached accounts were accessed this way), a breach on one site hands over the keys to all your others.
That shared phone or cyber café computer. In Tanzania and across East Africa, it's common to borrow a phone, use a shared device, or log in from a cyber café. If you logged into Facebook at a cyber café in Kariakoo and forgot to sign out, that account is still open — sitting there for anyone who uses that computer next.
SIM swapping. A particularly nasty trick where someone convinces your mobile network provider that they are you and gets your number transferred to their SIM card. Suddenly, every SMS verification code — including the ones that protect your M-Pesa and banking apps — goes straight to them. SIM swapping is growing rapidly as an attack method, accounting for 14% of social media compromises.
Third-party apps you forgot about. Remember that quiz app you authorised three years ago? Or that tool that promised to show you who viewed your profile? Some of those apps still have access to your accounts — and if they get hacked, your account goes with them.
Warning Signs Someone Is Already Inside
Sometimes your account talks to you. You just have to listen.
Your friends are asking about messages you never sent. This is Amina's story, and it's one of the clearest red flags. If people are receiving links, requests for money, or strange posts from your account — assume the worst and act immediately.
You're getting password reset emails you didn't request. Someone is trying to lock you out. This is a common early warning sign that a hacker has your email address and is probing your account.
You're randomly logged out of platforms. If someone else logs into your account and changes the password, your existing session gets kicked. Being unexpectedly logged out — especially from multiple platforms — is a quiet alarm bell.
Your settings have changed. Recovery phone number looks unfamiliar? Profile photo different? Language suddenly changed to something you don't speak? An intruder often adjusts settings to make themselves harder to remove.
Fewer emails in your inbox than usual. This one is sneaky. Hackers sometimes set up email forwarding rules to redirect your incoming messages to their own addresses — so you never see alerts about suspicious activity. If your inbox feels unusually quiet, go check your forwarding settings right now.
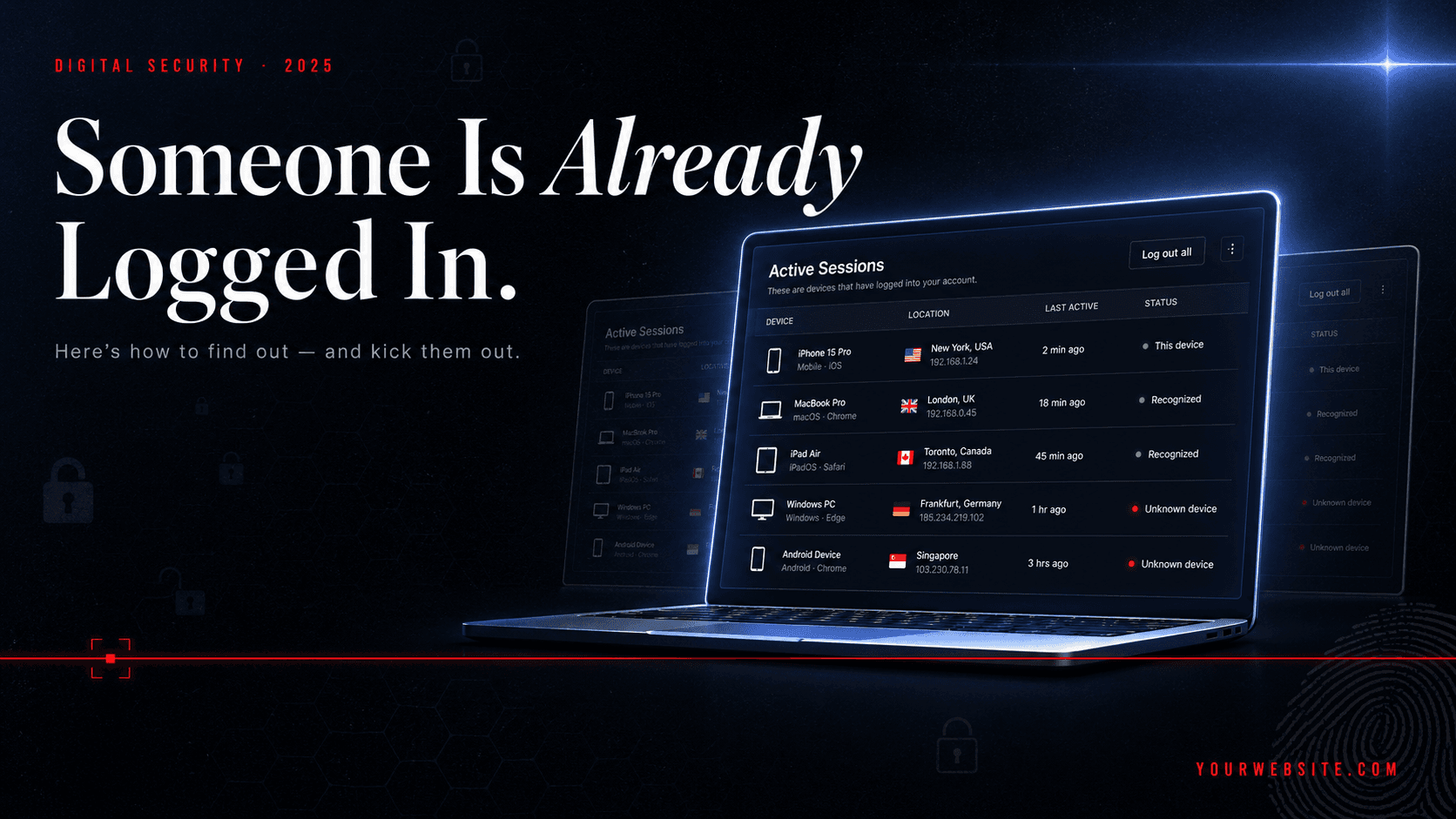
How to Check Right Now — Platform by Platform
Enough context. Let's get practical. Here's how to see exactly which devices are logged into your accounts, and how to throw out anyone who shouldn't be there.
🔵 Google Account (Gmail, YouTube, Google Drive)
Your Google account is the master key. If someone has this, they potentially have access to your emails, documents, photos, and any other app you've signed into using Google.
How to check:
- Go to myaccount.google.com
- Click Security in the left menu
- Scroll to Your devices and click Manage all devices
You'll see every phone, computer, and browser that's currently — or recently — signed into your Google account, along with their location and last active time. Google also lets you check at google.com/devices directly.
Don't recognise a device? Click it and select Sign out. Then immediately change your password and turn on 2-Step Verification.
🔵 Facebook / Meta
Facebook stores a surprisingly detailed record of every login — including the city, device type, and time.
How to check:
- Open Facebook and tap the hamburger menu (three lines)
- Go to Settings & Privacy → Settings
- Tap Password and Security
- Under Where You're Logged In, you'll see every active session
Facebook does an accurate job of recording your recent logins, including the approximate location based on IP address. If you see a city you haven't been to, or a device you don't own — tap it and select Log Out.
Important note: If you've ever used a VPN, that session will show the VPN server's location, not yours. Cross-check the login time before panicking.
WhatsApp works a little differently. Because it's tied to one primary phone number, it doesn't show a history of logins. But it does show you if your account is active on other devices.
How to check:
- Open WhatsApp
- Tap the three dots (top right) → Linked Devices
You can see if your account is active on multiple devices via WhatsApp Web or the desktop app. If you see a device you don't recognise, tap it and select Log out.
This matters because WhatsApp Web sessions stay active indefinitely — if you scanned the QR code on a work computer or a friend's laptop and never logged out, someone else may have been reading your messages for months.
How to check:
- Open Instagram and go to your Profile
- Tap the menu icon (three lines, top right) → Settings and Privacy
- Go to Accounts Centre → Password and Security → Where You're Logged In
You'll see a list of active sessions with device type and location. Any unfamiliar device names or locations are a sign of trouble. Tap any suspicious session and log out remotely.
⚫ TikTok
TikTok doesn't offer the most robust session management, but you can still check.
How to check:
- Go to your Profile → tap the hamburger menu
- Go to Settings and Privacy → Security
- Tap Manage devices
You'll see devices that have been used to access your account. Remove any you don't recognise.
🐦 X / Twitter
How to check:
- Go to Settings and Support → Settings and Privacy
- Tap Security and account access → Apps and sessions → Sessions
You'll find all current and past active sessions. Review them carefully — and log out of any sessions you don't recognise.
You Found a Stranger. Now What?
Don't panic. But move fast. Every minute counts.
1. Change your password immediately. Make it long (at least 12–15 characters), unique, and something you've never used before. The FTC recommends using a passphrase — a series of random words — which is both strong and memorable.
2. Sign out of all devices. Most platforms have a "Sign out of all sessions" or "Log out of all devices" option. Use it. This kicks the intruder out immediately.
3. Turn on Two-Factor Authentication (2FA) right now. This adds a second lock on your door. Even if someone has your password, they can't get in without a code from your phone. You can find this under the Security settings of every major platform. Google's own guidance calls this the single most important step you can take.
4. Check your recovery details. Make sure the recovery email and phone number on file are yours. Hackers often change these to lock you out permanently.
5. Check for email forwarding rules. If your email was compromised, go to your Gmail settings and look under Forwarding and POP/IMAP. Delete any forwarding addresses you didn't set up yourself.
6. Report it to the platform. Every major platform has a process for reporting compromised accounts. Use it — not just to recover your account, but to help them identify the source of the attack.
Lock the Door For Good
Checking your sessions once is good. Making it a habit is better. Here's a simple security routine that takes almost no time:
Use a password manager. Tools like Bitwarden (free) or Google's built-in password manager generate and store strong, unique passwords for every site. You only need to remember one master password. This single habit eliminates the 31% of hacks that happen through credential stuffing — where hackers try your leaked password from one site on all your other accounts.
Enable 2FA everywhere. Especially on Google, Facebook, WhatsApp, and your banking apps. Use an authenticator app like Google Authenticator rather than SMS codes when possible, since SIM swapping can intercept text messages.
Always log out on shared devices. This is especially important for anyone in East Africa who uses cyber cafés, shared phones, or office computers. Don't just close the tab — log out completely.
Check if your email has been in a breach. Visit haveibeenpwned.com — a free tool that tells you whether your email address has appeared in any known data breach. If it has, change that password immediately on every platform where you use it.
Make it a monthly habit. Put a reminder in your phone. Once a month, spend five minutes reviewing active sessions on your most important accounts — Google, WhatsApp, Facebook, and your mobile banking app. Think of it like checking the locks on your house before you sleep.
You Are Not Powerless
Here's the truth about account security that no one tells you: 94% of data breaches are caused by human error — which means the vast majority are also preventable by human action.
The hacker sitting in a café somewhere, running automated tools across millions of accounts, is betting that you're too busy, too trusting, or too unaware to check. Proving them wrong takes less than ten minutes.
Go check your sessions right now. Start with Google. Then Facebook. Then WhatsApp.
And when you're done, send this article to someone you care about — a parent who uses mobile banking, a sibling who's always on TikTok, a friend who still uses the same password they created in 2015. Digital safety is not a luxury for tech experts. In East Africa in 2025, it's a basic survival skill.
Stay safe out there. The internet is an incredible place — but only if you know who has the keys to your corner of it.